Authentication Vs. Verification: What’s the Difference?
Published: May 19, 2023
Updated: Apr 16, 2025
The matter of authentication vs. verification is one that’s gaining quite a bit of traction.
The two terms are very often used interchangeably.
To an extent, they’re even similar in definition.
But when it comes to the digital world, they’re not exactly the same, even though they serve one purpose—to protect digital identities.
With the increase in online business activities, the web has become a lucrative environment for data breaches.
One such method is SMS phishing.
This is where attackers use text messages to trick users into revealing sensitive data or downloading malicious software.
That being said, both authentication and verification have become major tools in business text messaging to validate users and prevent fraud.
Identity Verification Vs. Authentication: Getting to Know Each
Before exploring the difference between authentication and verification, you must understand what each of them means.
Keep in mind that they are two sides of the same coin—they are different yet share the same motive.
What is Authentication?
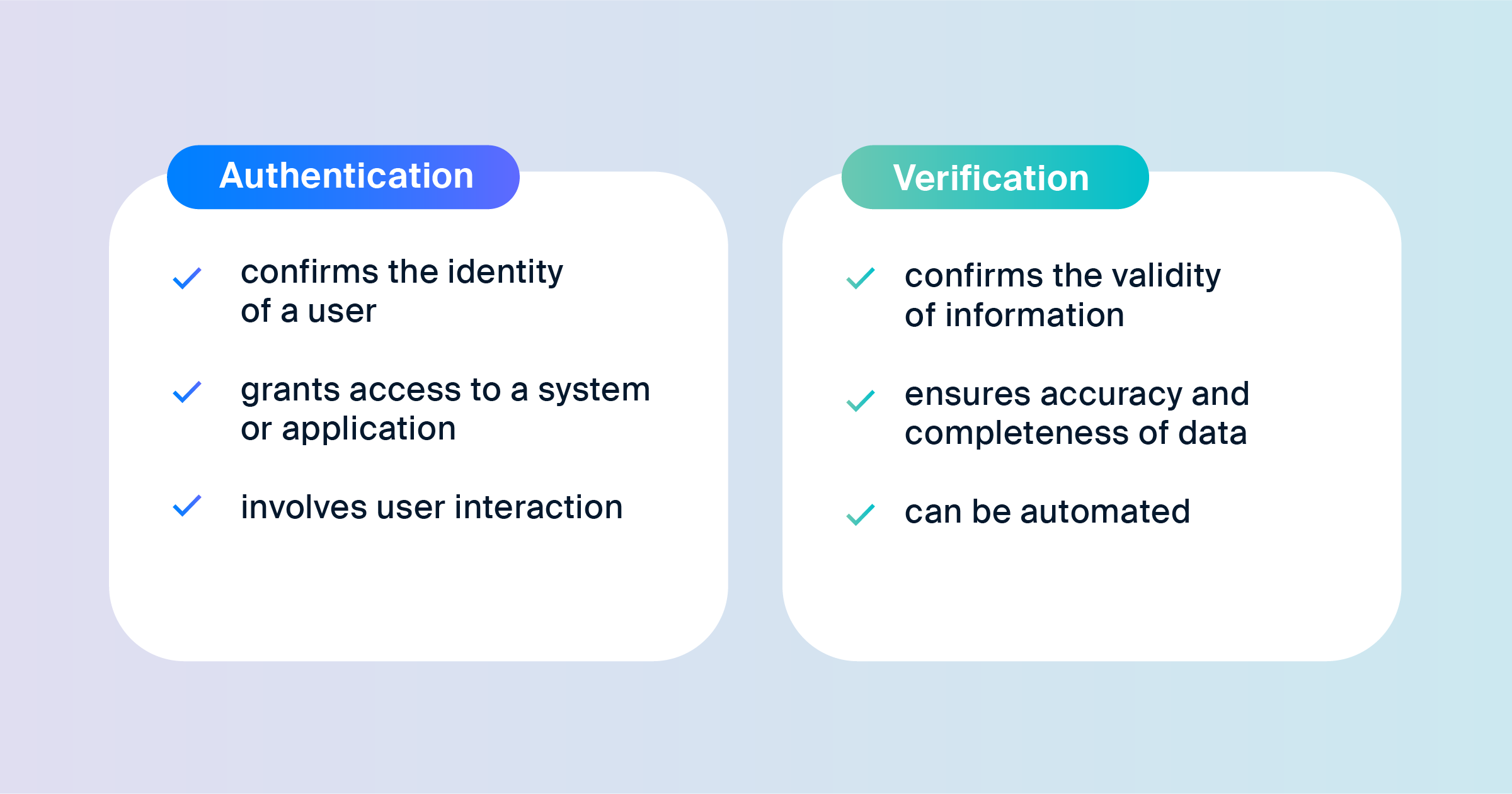
Authentication is when the system ensures that a user accessing an account is its rightful owner.
It does so by validating the online identity of the user via a unique code.
The process involves making use of details that the user initially provided.
Identity authentication takes place every time a person wants to use a company’s application.
It works by asking for a password or requesting passwordless authentication like sending an OTP SMS, flash calling, or demanding a fingerprint.
This essentially prevents fraudsters or unauthorized individuals from breaching genuine accounts for illegal reasons.
Get Started Now
Reach your clients now and claim your 30-day free trial. No credit card required.
For instance, HIPAA regulations require practitioners to authenticate their identity before accessing sensitive patient information.
There are three different categories of authentication:
Security Information: Also referred to as a knowledge-based challenge, this requires the customer to enter info that only they would know. The system then compares that information to the one given previously by the user. This can be a username and a password or an answer to a question like “What is the first school you went to?”
Security Devices: This authentication method involves authenticating customers through a device of their own—in most cases, a mobile phone. The application would ask the user to enter a one-time password sent to that device. A common example of this is an SMS verification code or another form of two-factor authentication.
Biometric Data: With the biometric data approach, the application authenticates users through biometric factors such as fingerprints, facial recognition, or iris recognition. You may be required to take a photo of the system to compare it with the one you provided previously.
What is Verification?
Now that you’re familiar with the former, it’s worth getting to know the other side of verification vs. authentication.
Verification is the process of confirming a digital identity and often takes place at the beginning of a relationship between a user and a company.
This occurs during the onboarding process.
The company may request a user’s phone number and date of birth, maybe even a passport or a driver’s license.
This is done to make sure new users are indeed who they claim to be.
The extent of verification can also range from asking for an email address to digging into credit checks. To enhance this process, businesses can use solutions like Dexatel’s OTP SMS service, which help validate a user’s phone number, ensuring its authenticity and reducing the risk of fraud right at the beginning of the customer journey.
The company would then validate the information or the documents with a third-party or authoritative data source, normally through digital verification solutions.
These solutions validate the ID in two different ways:
ID Verification: This method involves checking official documents such as passports and bank statements for various features like fonts, stamps, and watermarks. Such features are meant to verify the authenticity of a document.
Identity Checking: This is where personal information, like name and postal address, is checked against third-party sources. There are two ways to access this information: either through official identity documents or by the customer.
Verified identities help in minimizing the risk of fraudulent activities taking place during the onboarding or subscription process.
However, the purpose of verification solutions extends beyond fraud prevention.
The practice is also crucial when you need to guarantee compliance—for instance, if you’re an online retailer that sells age-restricted products like vapes.
The Difference Between Authentication and Verification
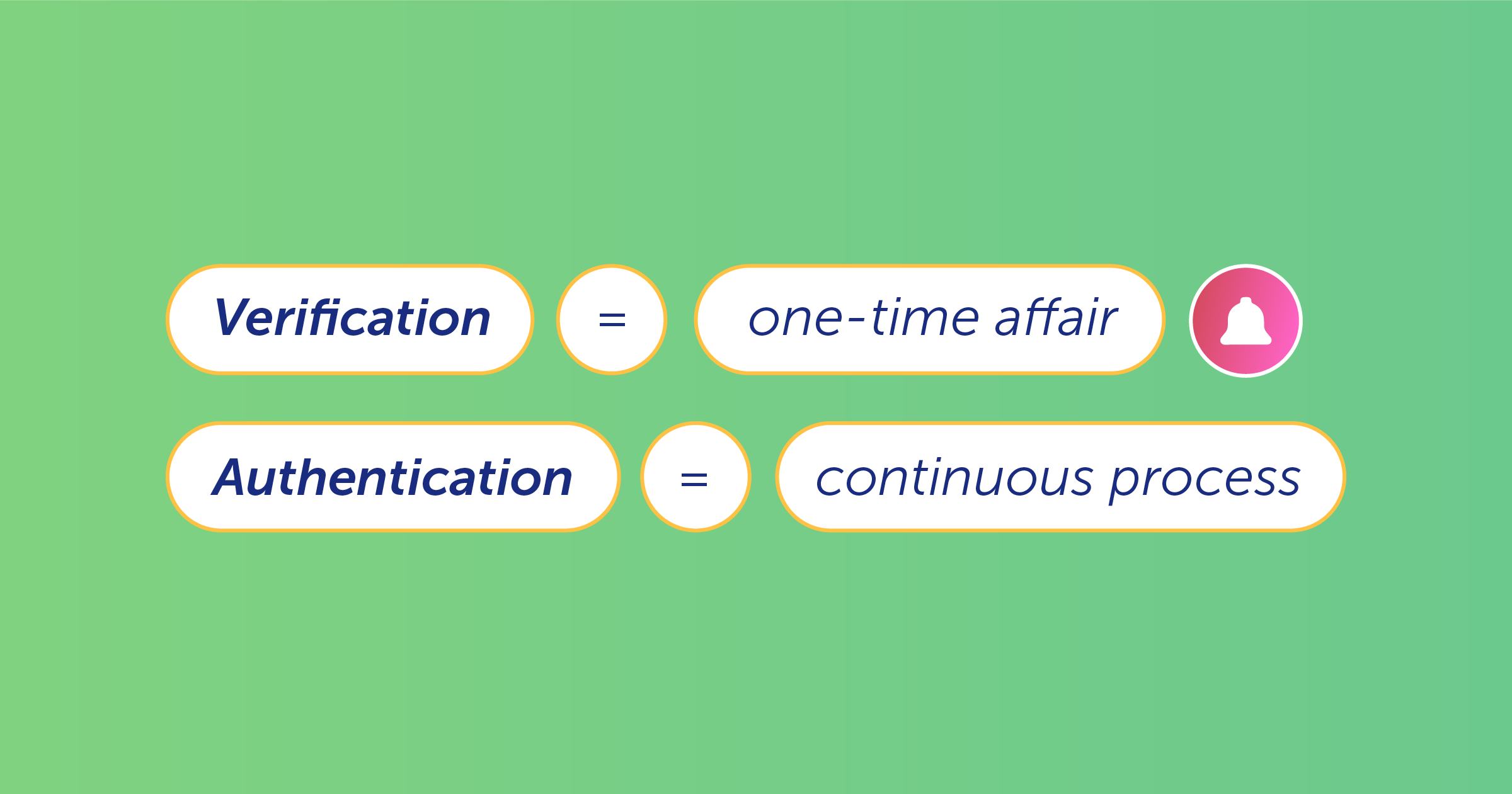
Although they both aim to protect digital identity, there is a clear difference between authentication and verification.
Authentication guarantees that a user trying to access an account has permission to do so.
On the other hand, verification validates that the information that the user provided is indeed authentic.
And while verification is only performed once, authentication needs to take place each time a user logs in.
Determining the amount of information you need to verify and in what cases you need to authenticate depends on a number of factors.
It involves knowing the regulations of the industry you’re in as well as those of the country itself.
You’ll also want to assess the risk profile of the products or services you offer in addition to the risk profile of your customers.
In the financial sector, for example, regulations require you to verify considerably more information than registering customers for a fast food service account.
In the latter scenario, a password and maybe a security question would be enough.
But let’s suppose you’re opening a bank account for a new client.
You’ll need a set of official documents in addition to biometric data, security devices, and personal information.
Another example would be the European Union’s PSD2 authentication requirements.
These essentially determine how you should authenticate commercial transactions and monetary exchanges that occur inside the EU.
Authentication Vs Verification: Latest Trends
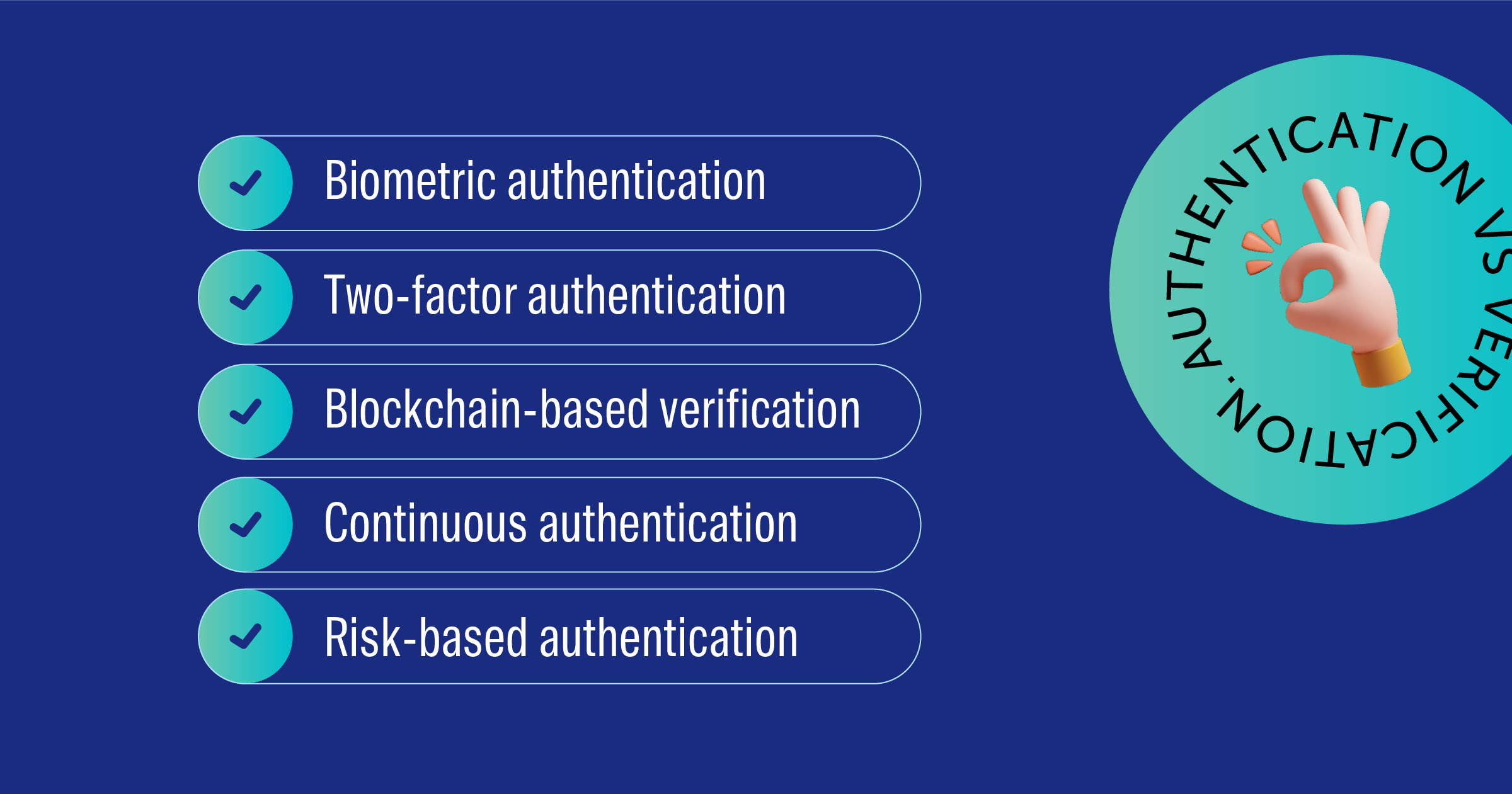
With our online presence increasing on different fronts, the risk of cyberattacks looms more than ever before.
As a result, identity verification and identity authentication practices are becoming the norm.
We’re also seeing trends that indicate what measures businesses should take to meet cybersecurity needs.
Risk-Based Methods
Authentication is trickier than it may seem. The more factors you incorporate, the more you’ll guarantee a user’s legitimacy.
But asking users to go through multiple steps each time they want to access their account can ruin the customer experience.
Bringing artificial intelligence into the mix, however, can pinpoint the risk and build trust between you and the user.
In this case, the system would only request authentication when there is an elevated level of risk.
Rethinking Strategies
The past couple of years have seen a significant uptick in online transactions, partly due to the global pandemic.
And with online presence comes vulnerability.
This has prompted businesses to rethink how they manage digital identities.
As a result, digital identity verification checks are expected to triple until 2026, according to research by Goode Intelligence.
Safety Comes First
Would you personally trust an application that doesn’t have security measures in place?
Customers are becoming aware of how data-intensive their subscriptions have become, and are seeing the potential security risks.
They are also skeptical about businesses that don’t take the necessary measures to prevent fraud and identity theft.
And not offering that element of safety is a perfect way to lose customers.
Key Takeaways
As technology continues to evolve, so too must our methods for securing it.
It is imperative that businesses remain vigilant and adaptable in their approach to authentication and verification and that they continue to educate their customers on the importance of these processes.
Only then can we hope to create a safer, more secure digital environment for everyone.
