What is SMS Spoofing and How to Prevent it
Published: Sep 13, 2019
Updated: Jul 12, 2023
While SMS is a new technology, spoofing and smishing have been around for a while.
Remember when your friends pranked you by saying your crush sent you a love letter?
Then you found out it was actually your friends who wrote the letter.
That’s a classic example of the act.
Nowadays, instead of papers, people fall victim to SMS spoofing.
Since text messaging is a casual and convenient communication channel, it’s susceptible to spoofing.
What Is SMS Spoofing?
SMS spoofing is a technique where people replace or alter the originating mobile number of a text message with an alphanumeric text of their choice.
In other words, people change their ID, phone number, or even both.
How Does SMS Spoofing Work?
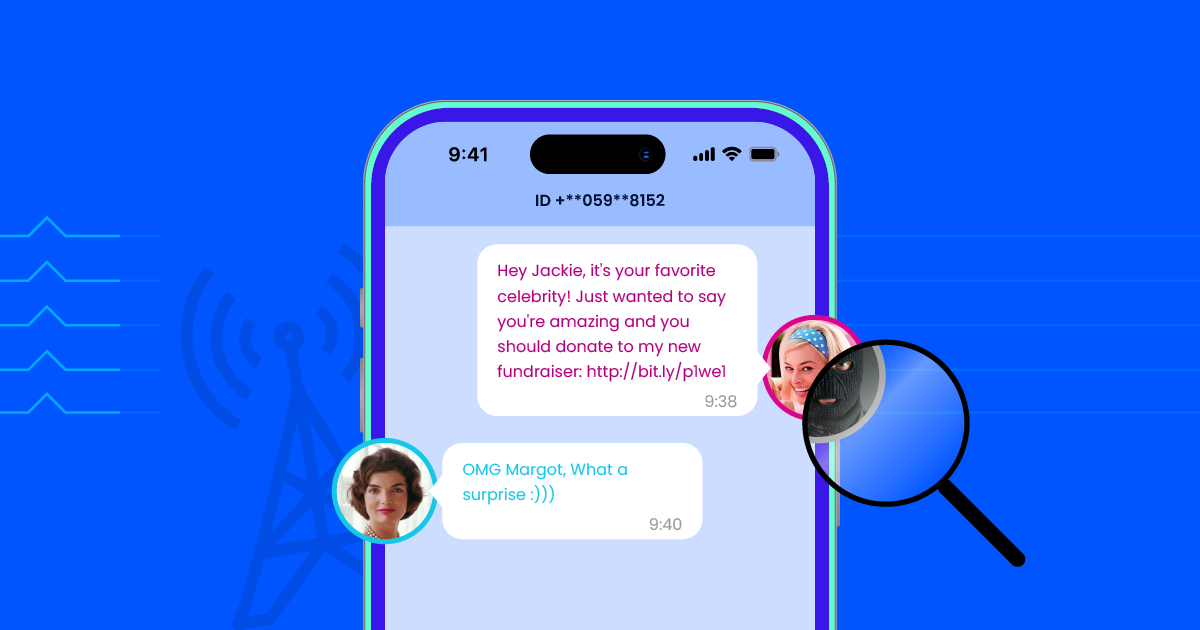
Targets receive text messages under the assumed identity of other companies or familiar mobile phone users or numbers.
In fact, it is perhaps the ideal tool to conduct fraudulent activities.
It masks the identity of the sender and replaces it with an identity they’re trying to imitate.
As a result, a lot of scammers try to phish for personal information such as bank accounts, credit card details, and fake money transfers using such attacks.
How to Detect Spoofing Messages
Certain signs may point towards a text message being fraudulent.
Being able to identify a fake text message can help you avoid falling victim. Here are common signs to watch out for:
1. Suspicious Terminology
When it comes to SMS spoofing, the text will often bring up suspicious situations, using terms like “delivery attempt,” “account deactivated,” and “immediate action required.”
2. Unrecognizable Phone Number
The sender ID may sometimes look like an ordinary phone number.
If you don’t recognize it, consider looking it up—even if the message claims to be from a reputable company.
3. Grammar and Spelling Mistakes
Scammers usually misspell words on purpose to bypass spam filters that look for specific words.
They also do this because recipients who don’t pay attention to spelling mistakes tend to be less watchful and are more likely to fall victim.
4. Unclickable Sender Field
The field containing the sender's identity and name will not be clickable and will have a gray shade.
In regular messages, this will be blue, and you should be able to click on it.
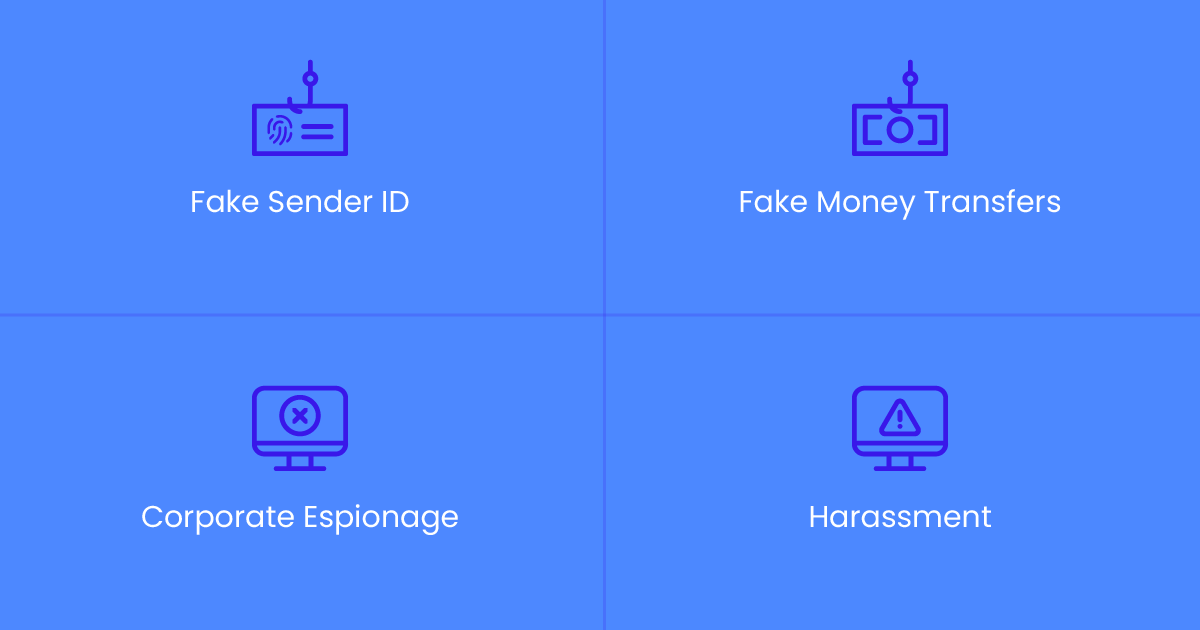
Types of Spoofing SMS Messages
Spoofing text messages come in several different forms, but often with the same intent of accessing personal information or stealing money.
In other words, an SMS spoofer may use various approaches to get whatever it is they want.
1. Fake Sender ID
The most common form of text message spoofing is when the scammer replaces the actual sender ID with a fake one.
This enables them to appear as a trusted organization that the recipient might be affiliated with, such as a bank, an insurance company, or a credit card service provider.
Using a fake sender ID can be a highly effective and effortless way for the scammer to obtain information.
Suppose you know when a person’s health insurance will run out and that they will need to renew it.
As a text spoofer, you would use that information to trick the person into entering a link where they could supposedly “renew their plan.”
Instead, they would be redirected to an unrelated website and consequently fall victim to a scam.
Example: “Urgent action needed: Your health insurance has expired. Please renew your plan as soon as possible to avoid extra fees by clicking here: http://bit.ly/p1we1”
2. Fake Money Transfers
Another type of text messaging or SMS spoofing work involves telling the recipient they’ve won a prize.
The fraudster would then ask the recipient for their bank account information in order to “transfer the amount.”
In other cases, a scammer might pretend to be a banking institution and send a message to potential victims about a fake cash-back transaction.
This form of smishing text typically asks the user to claim the amount by accessing a link or scanning a QR code.
Example: “Dear user, your credit card points worth $1,234 will expire today. Please redeem your cashback by clicking here: http://bit.ly/p1we1”
3. Corporate Espionage
As the name implies, corporate espionage is a type of SMS scam that involves spying to steal company information.
Employees would receive a text message that included a URL to a malicious website.
Once the recipient clicks on the link, it redirects to a different site, which would then install malware to collect and steal sensitive information from the person or business.
Hackers often practice corporate espionage for the purpose of accessing company resources.
Needless to say, such phishing attacks can cause damage to an enterprise.
Example: “Attention! Your account has been deactivated. Click here to restore your login information: http://bit.ly/p1we1”
4. Harassment
Stalkers and scammers use this form of text spoofing to send unwanted or threatening messages to people.
In many cases, they do this to extort money from the recipient—often with the threat of consequences if the money isn’t paid.
Scammers may also use scare tactics, such as family emergencies to urge you to take immediate action.
For instance, you may receive a message saying that a relative is having surgery and needs money as soon as possible.
Example: “Hi, your cousin is in the hospital due to a car accident and needs money urgently. Please transfer $800 to this account now: 123456789”
How to Prevent SMS Spoofing
Chances are you’ve received your fair share of spoofed messages before—we all have.
It’s also likely that you may receive some in the future, too.
Knowing how to dodge SMS spoofing attacks is crucial; you’ll be protecting not only your personal information but also a great deal of your money.
And all it takes is a few simple measures.
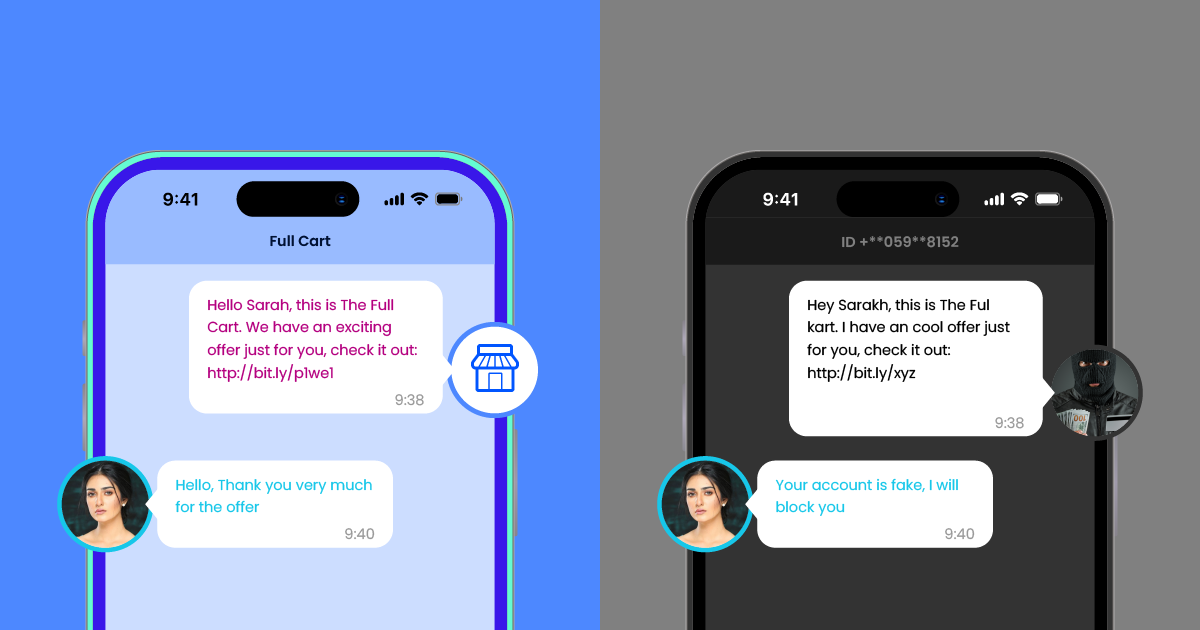
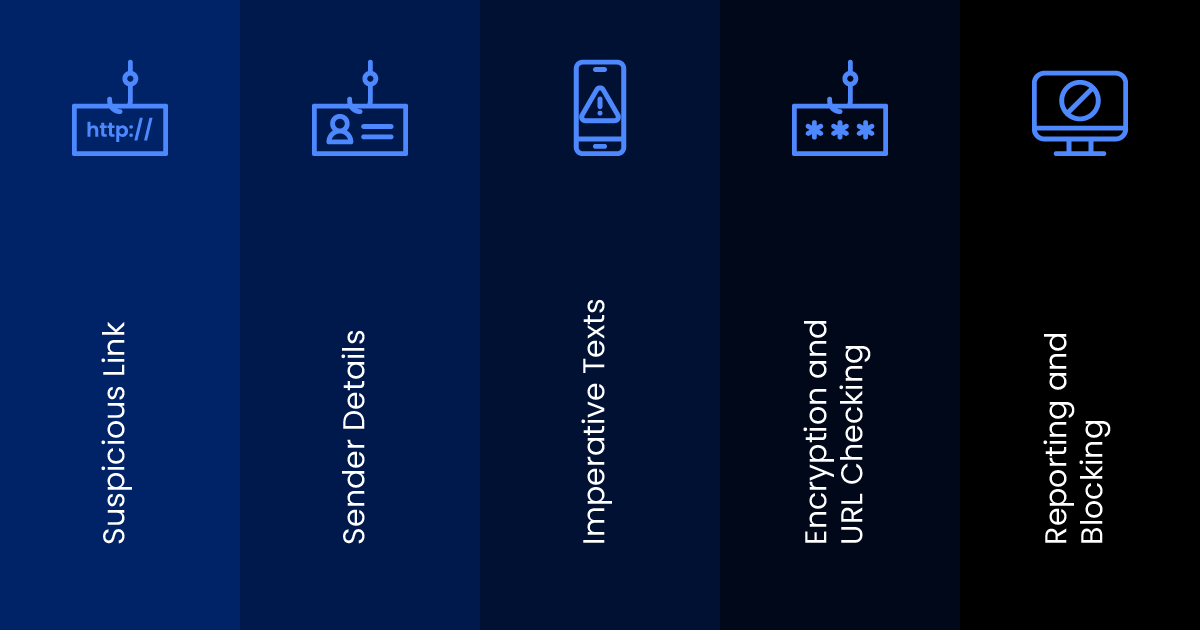
Always Examine Sender Details
Always keep an eye out for subtle spelling errors in the sender ID or number.
Scammers will often make these small changes intentionally to trick inattentive recipients.
Suppose your bank is called State Holdings.
You may, for instance, receive a phishing message impersonating the bank but with the sender ID “State Holding” (without the ‘s’ at the end).
Minor details like this one should be a dead giveaway of a spoof text message.
Avoid Replying to Imperative Texts
Scammers may often use the element of urgency to prompt you into doing as they ask.
This is because recipients are more likely to detect the sham if they take their time.
Always be suspicious of unsolicited text messages that tell you to take immediate action.
And let’s be honest; why would your “cousin” want you to transfer an unreasonable amount of money out of nowhere so they can “get out of prison?”
Check for Encryption Before Entering a Link
Unencrypted URLs in SMS spoof text messages are another indicator of a text scam.
Links that appear overly long or short—or consist of strange character strings—are grounds for suspicion.
Be aware of hyperlinks that start with HTTP instead of HTTPS, as this can signal a lack of encryption.
This is where an online URL scanning tool would come in handy.
Simply copy the suspicious link you received via SMS and paste it on a website like Google’s VirusTotal.
No one can be 100% safe from spoofing and smishing attacks.
Whether scammers attack you or use your number for that purpose, you should always report it to your carrier and law enforcement, who can track where the SMS phishing messages came from.
This way, you can prevent it from happening in the future.
You can also download SMS blockers to make sure that you won’t receive an SMS from the scammer a second time.
The Legality of a Spoofed SMS Message
You might think that these instances create a solid ground for illegalizing the practice.
However, the gray area lies within the anonymity of senders.
What if someone wants to whistleblow without having their identity exposed?
What if you wanted to pull a harmless prank on your colleague?
At the end of the day, there’s no black or white—as long as you’re not doing it with malicious intent.
Nevertheless, all this makes it even harder for authorities to detect and deal with the situation.
But, one thing is clear—Using it under false pretenses is illegal in many countries and can get you in a lot of trouble.
There is no clear legislation about spoofing text messages in the majority of countries.
Some have proposed banning the practice altogether, while others are negligent regarding the issue.
Australia is a notable example of a country that has completely prohibited the practice of spoofing.
In countries where it is not regulated by national authorities, carriers have taken the matter into their own hands by banning the anonymous use of spoofed texts.
